How & who
Connect channels and systems without flattening access across your org
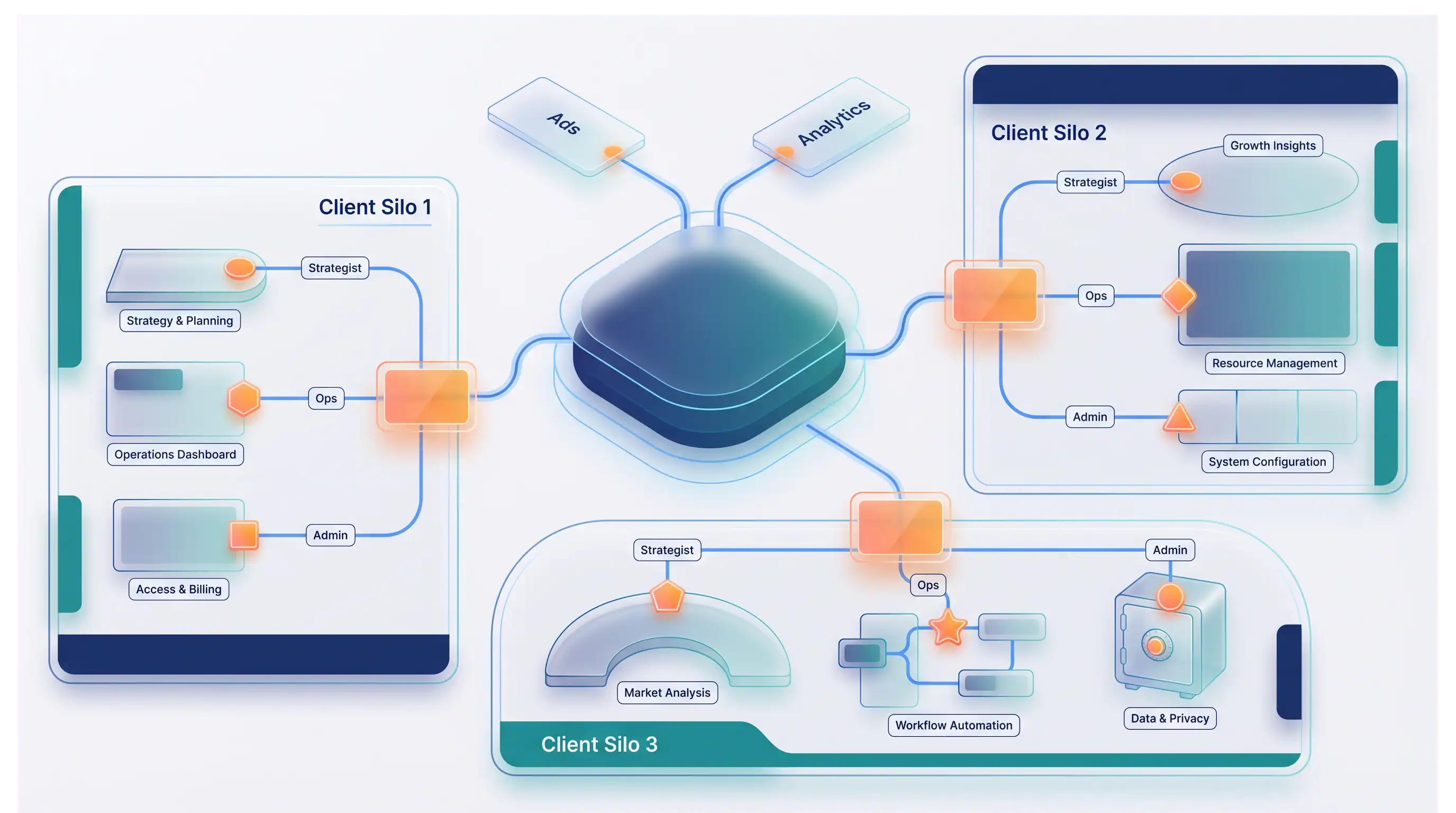
Integrations exist to feed planning and reporting—not to bypass client boundaries. Synapic treats connectors as scoped: who may use which accounts, how data enters workflows, and where to audit usage when stakeholders ask.
Outcome
Operational confidence: predictable data handling, not surprise exports
In practice, integration work means answering ‘who had access?’ and ‘what did we connect for this client?’ Synapic’s model keeps those answers adjacent to execution—alongside privacy, subprocessors, and security resources when procurement joins the thread.
Capabilities
What teams connect first
- Google Ads and analytics data connectors
- Meta campaign and audience data flows
- Client-level access control for integrated resources
- Governed ingestion and scoped usage across teams
That shows up day to day as fewer ‘mystery spreadsheets’ and fewer debates about which integration fed which number—because scope and ownership are explicit from the start.


Governance in the loop
Connected systems without compromising accountability
Connect intentionally—scope sources and access paths to match ownership boundaries. Validate continuously so integration health stays visible next to decisions. Execute confidently with controls embedded in workflows, not as an afterthought.
Data rights matter too: when someone asks how deletion or retention works, the answer should not require a separate thread. Subprocessors · Privacy policy · Data deletion
Implementation sequence
From selection to operational insights
- 01
Select sources and scopes
Define which accounts, clients, and entities should connect—and what each role may access.
- 02
Apply access controls
Configure permissions and safe defaults before activating workflows that consume integrated data.
- 03
Operationalize insights
Feed trusted signals into planning, execution, and reporting loops with traceability intact.
Proof
Scoped by client and role
Integration access mirrors how you separate accounts in real life—not one shared key for everyone.
Traceability when it matters
Usage and ownership patterns support operational reviews without guesswork.
Trust docs in reach
Security, subprocessors, and privacy sit beside the workflows that consume data.
Need a specific connector or rollout plan?
We can help map requirements, sequencing, and access boundaries for your stack.