Proof & risk reversal
Trust artifacts your buyers expect—published, organized, and easy to share
Security posture, subprocessors, privacy, terms, cookies, and data deletion should not be a scavenger hunt. Synapic centralizes what procurement, IT, and legal typically ask for—so delivery teams can keep momentum.

What this means in practice
Auditability and data rights are part of the product story—not an appendix
In real deployments, ‘trust’ is a set of concrete questions: who can access what, how providers are used, how to request deletion, and where policies live. This hub exists so those answers are one click away—parallel to the work that depends on them.
Trust resources
Everything stakeholders expect in one place
Navigate from the question to the artifact: security principles, subprocessors, privacy, terms, cookies, and data deletion—each with a stable URL you can forward internally or to a client contact.
- SecuritySecurity principles and operational safeguards for the platform.
- SubprocessorsCurrent subprocessors and the service categories they support.
- Privacy PolicyHow data is handled, retained, and protected.
- Terms of ServiceService terms, responsibilities, and usage policies.
- Cookie PolicyHow we use essential and analytics cookies.
- Data DeletionControls and requests for account data deletion.
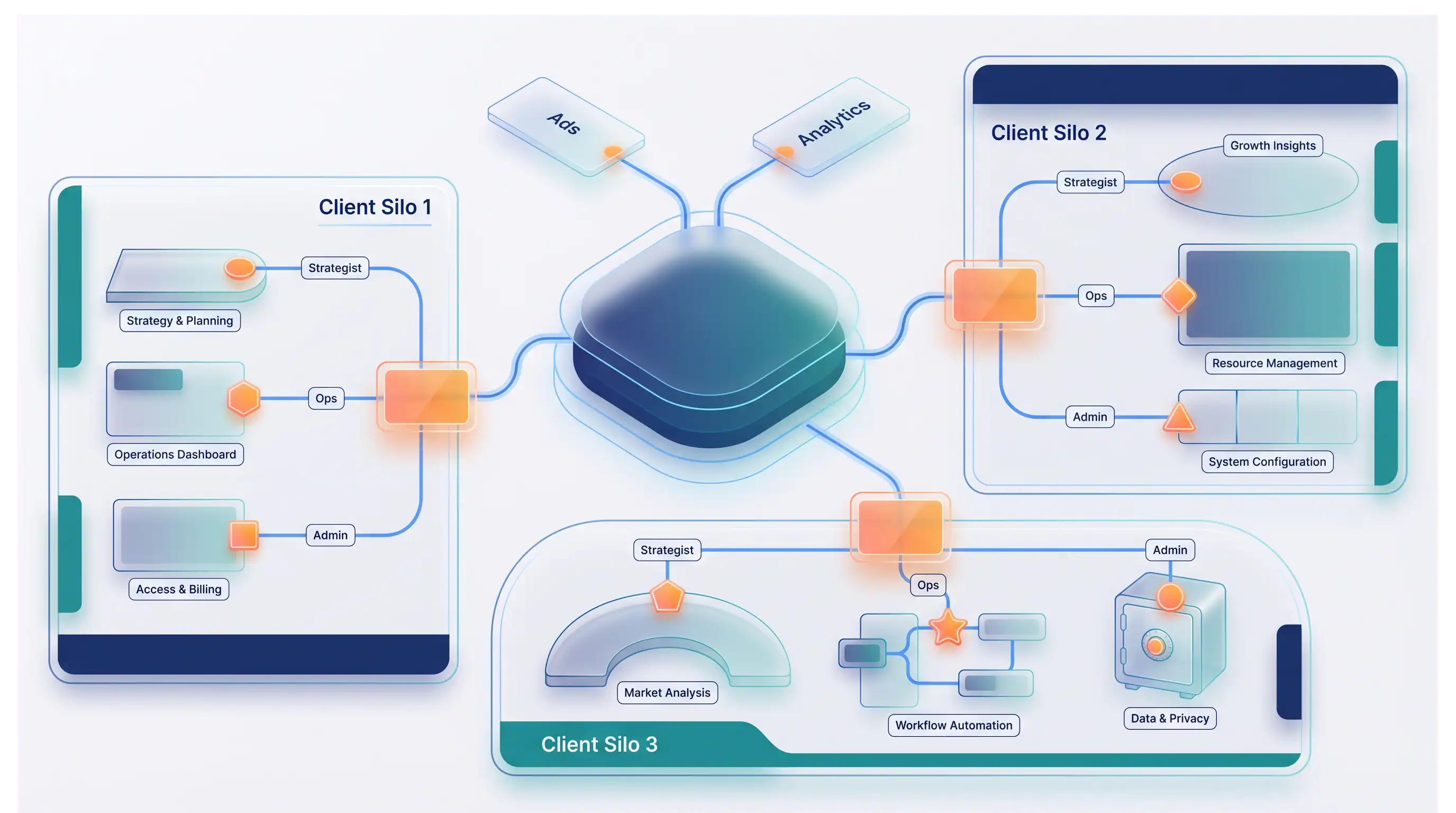
In-product posture
Credibility that scales with complexity
Visibility by design: public trust resources reduce friction in procurement. Controls in context: governance stays connected to operational delivery paths. Responsible execution: data rights and deletion pathways stay explicit and accessible.
How we keep trust current
Publish, apply, update
- 01
Publish standards
Document policy and operational expectations in resources teams and clients can actually use.
- 02
Apply controls in workflow
Map security and privacy patterns to daily execution—not separate checklists.
- 03
Maintain transparent updates
Keep trust documentation aligned as capabilities and subprocessors evolve.
Who this helps
Procurement & IT
Faster answers on providers, access models, and policy without blocking campaigns.
Delivery leads
Less time translating security emails into action items for the team.
Client-facing teams
Credible, linkable documentation when trust comes up in reviews.
Questions for security or procurement?
We will point you to the right documents—or walk through controls in the context of your rollout.